What is tcpdump?
TCP (Transmission Control Protocol) is a communication standard that devices use to talk establish communications between each other. The communication then takes place in packets. Normally a lot of the communication between devices is hidden away from us humans as we don’t need to see our computer ask a DNS server for the IP address for a website URL, then the sending of a GET command to the website IP etc.. when we load a webpage in our web browser.
tcpdump is a network packet analyser, which lets you see the conversation packets.
Installing tcpdump
When I tried to use the tcpdump command on Raspbian I got the message the command was not found. This is fixed with sudo apt-get install tcpdump.
tcpdump Commands
Note: You may need to use sudo before the commands if your user doesn’t have permission.
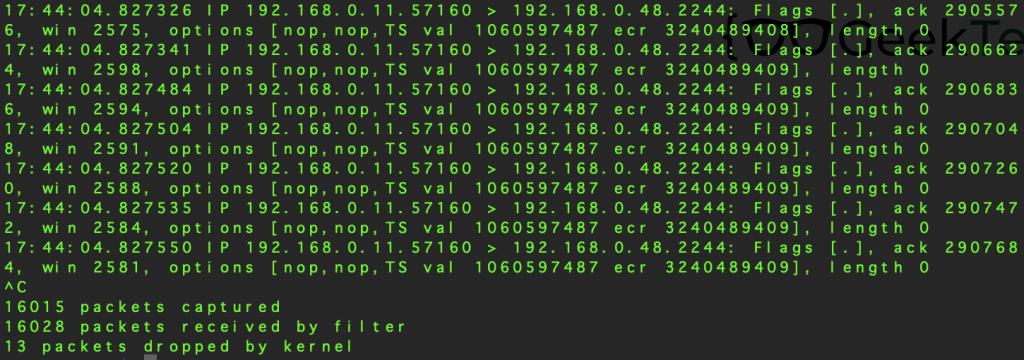
tcpdump starts tcpdump running, but be prepared for a flood of information if you run tcpdump without any arguments.

If you have multiple network interfaces (perhaps ethernet and wireless) then the -i command can be used to limit the packet dump to a specific port e.g. -i eth0 for the ethernet port, or tcpdump can be specifically told to listen to any port using -i any.
tcpdump -D can be used to view the interfaces available to tcpdump.

As the above screen grab shows, there may be more interfaces than you expect. If you know which interface your communication is taking place over then I would recommend limiting the packet dump to that interface.
With an interface selected (wlan0 aka my wireless adapter), the traffic selection can be limited further by telling tcpdump to watch traffic from a particular host.

In the above example tcpdump is listening on wlan0 for traffic from 192.168.0.1
If you do not know where the traffic is coming from, then you could limit the analysis to a particular port.

tcpdump -i wlan0 port 80 tells tcpdump to listen on my Pi’s wireless adaptor for traffic on port 80. The host and port options can both be used together to refine the analysis even further. This done by using the boolean “and” word.

tcpdump also supports the boolean “or” and “not” words.
Even with arguments to limit which traffic is analysed you may still get a lot of packets streaming past, which is why tcpdump has an option to save the details to a file using tcpdump -w FILENAME.pcap , replacing FILENAME with an appropriate name. The pcap file format can be open and examined in a program such as Wireshark (https://www.wireshark.org).
When using the -w argument you may want to limit how many packets you capture. This is accomplished using the -c argument. -c 100 will tell tcpdump to capture 100 packets.


You must be logged in to post a comment.