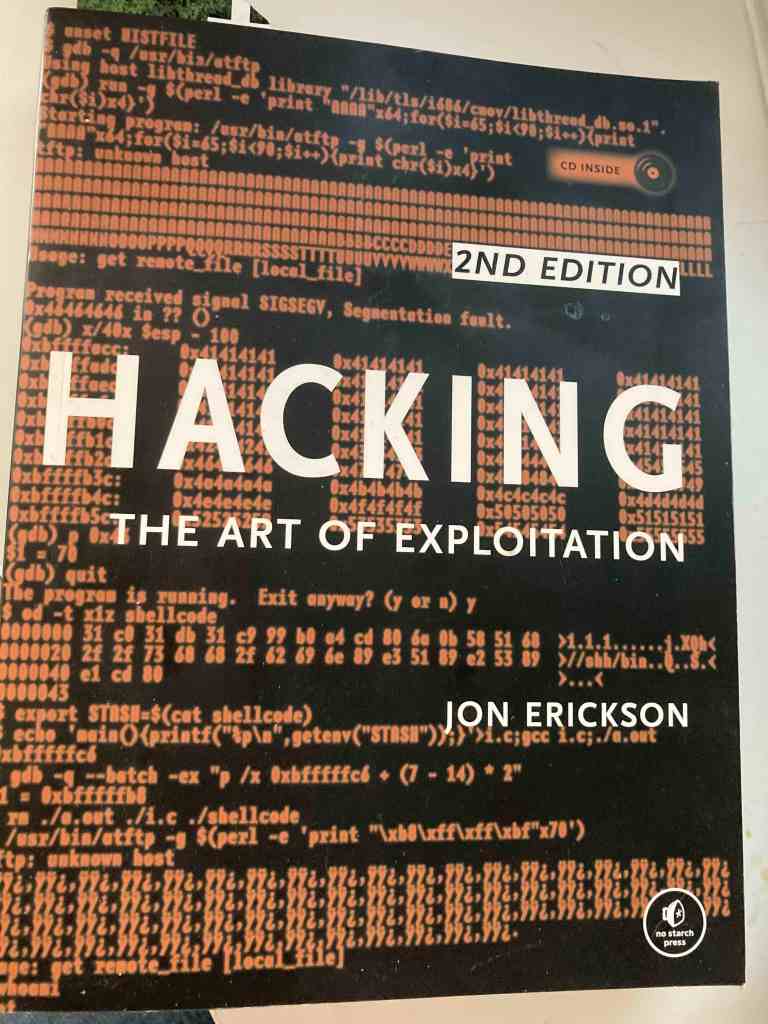
Hacking: The Art Of Exploitation (2nd Edition) was released back in 2008, written by Jon Erickson and published by No Starch Press. I originally received a copy as part of a Humble Bundle and purchased physical copy in 2019 (19th printing!), off the bat that should show how much I enjoy this book. The book is part of my degree’s Cyber Security module reading list, giving me another reason to (re)read it and to write a short review.
As the book was published in 2008 the CD accomplishing it is slightly out of date, however modern versions of Virtual Box and Ubuntu are both available online. No Starch Press also offer the programming code samples online as well at: https://nostarch.com/download/booksrc.zip Note: The book focuses an the x86 processor, so if you are using an x64 based processor or an ARM based processor prepare to be using Google at times to help.
The book is split into sections covering Programming, Exploitation, Networking, Shellcode, Countermeasures and Cryptography, bookended by an Introduction and a Conclusion.
Programming
Introduces pseudo code, C and assembly language. It is a brief introduction, and moves a quick pace. The processor registers are for the x86 processor, and this is where I really recommended further reading about the registers of modern processors. The chapter gives a brilliant overview into memory management, stack / heap management and using C to work with files.
Exploitation
Builds on the programming chapter to discuss and give examples of how overflow vulnerabilities can happen in the buffer, stack and with function pointers.
Networking
An overview of the OSI model and then it’s onto sockets and using C to interact with the layers in various ways. Packet sniffing with a C, building a basic web server and explanations of the RFCs around network technology. Syn Flooding, Ping of Death, Ping Flooding and Port Scanning are all covered as well. For anyone that has used tools such as WireShark or nmap this is a great chapter to get a better understanding of how they may be working under the hood.
Shellcode
Shellcode is the magic step that takes hackers to the next level, and it can be confusing. This chapter gets into Linux system calls, shellcode and null bytes. A good understanding of the Programming and Exploitation chapters are highly encouraged to understand this chapter.
Countermeasures
Detection techniques are a must to know if a system has been compromised, and for a hacker they are something to be aware of / avoid. This chapter looks at system daemons (which was named with a nod to James Maxwell’s thought experiment in 1867!), catching system signals, spawning a root shell, spoofing and Intrusion Detection Systems (IDS).
Cryptography
Symmetric and asymmetric encryption, Man in the Middle attacks and WEP are just some of the topics covered. This chapter teaches everything needed to know for a very firm footing in encryption techniques. Although technology like WEP is rarely used in 2022 it is still great to learn why it was created, and why it was superseded.
Hacking: The Art of Exploitation can be frustrating at times (due to the amount of knowledge being shared), and it can be a little confusing for those new to C. However, it’s also a book that rewards those that stick with it, that explore how to use it on modern processor architectures (or dig out an x86 machine) and that look at the differences of technologies between 2008 and 2022. It’s a title which I’ve returned to multiple times, and each time I’ve learned something new from it. If you want to understand how hacking works rather than just use someone else’s tools then this is the book for you.
The No Starch Press page for Hacking: The Art of Exploitation is available at: https://nostarch.com/hacking2.htm , with a sample (PDF) chapter at: https://nostarch.com/download/hacking2_sample.pdf

You must be logged in to post a comment.